Eckoh Appoints Tim DeLisle as Chief Revenue Officer to Accelerate Global Growth
12 Aug 2025
Eckoh is pleased to announce the appointment of Tim DeLisle as Chief Revenue Officer. DeLisle will lead Eckoh’s global revenue strategy to accelerate growth and scale the company’s presence, strengthening its position as a leader in secure customer engagement solutions.
Read moreBridgepoint completes acquisition of Eckoh
20 Jan 2025
Eckoh is proud to announce its acquisition by Bridgepoint, a leading private equity investor. This marks the beginning of an exciting new chapter, with Bridgepoint supporting our growth through innovation, expansion, and strategic opportunities to unlock our full potential.
Read moreUnaudited interim results for the six months ended 30 September 2024
20 Dec 2024
Eckoh is pleased to announce unaudited results for the six months to 30 September 2024
Read moreEckoh achieves the PCI DSS v4.0 standard for the 15th consecutive year
8 Oct 2024
Eckoh successfully achieves PCI DSS v4.0 certification for the 15th consecutive year, demonstrating its ongoing commitment to cutting-edge data security.
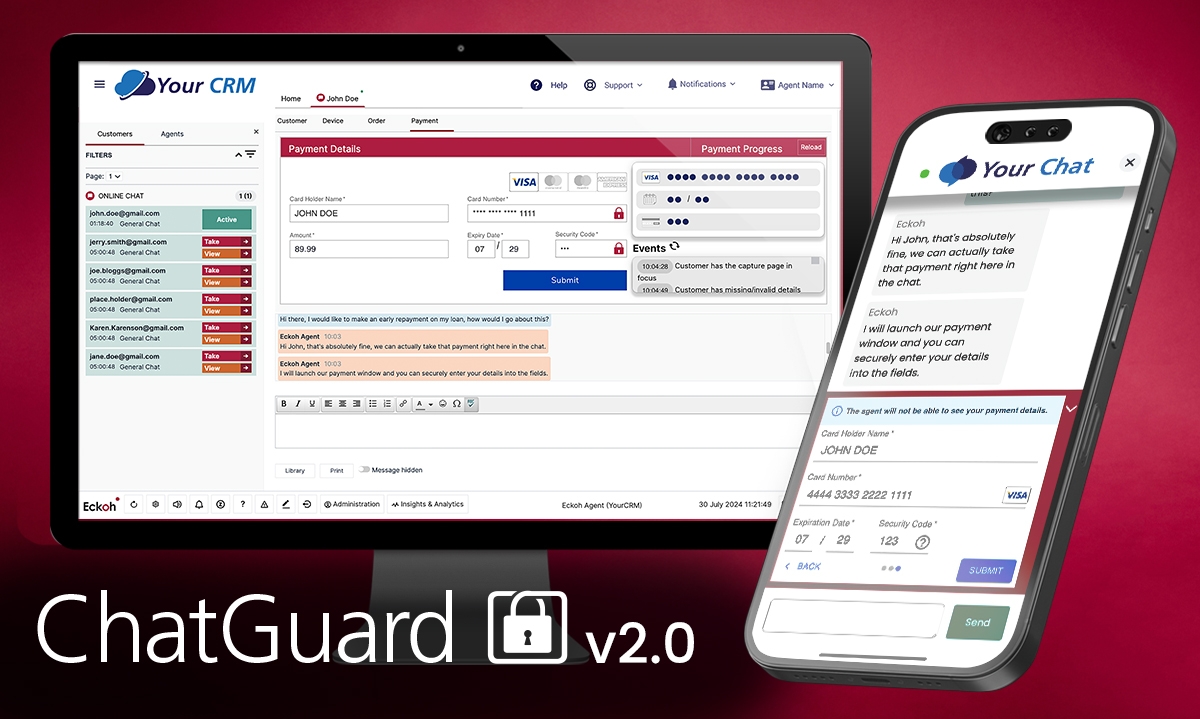
Read moreEckoh updates ChatGuard to add 3D Secure, digital wallets and PII
20 Aug 2024
Eckoh announces updates to ChatGuard, adding 3D Secure, digital wallets, and PII protection, enhancing secure payments and customer verification within chat.
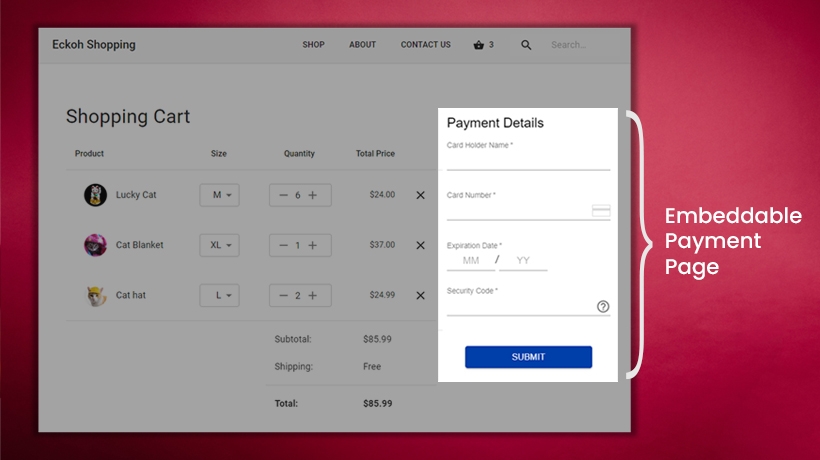
Read moreEckoh launches new embeddable payments solution
23 Jul 2024
We are pleased to announce the launch of our new embeddable payments platform
Read moreUS consumers raise concerns that home-based contact center agents pose a risk to their data security
25 Jun 2024
First-party research reveals that consumers will shop around if brands fail to meet their data security and privacy expectations
Read moreFull year results 2024
11 Jun 2024
Record new business in North America, up 44% to $16.8m, and total contracted business at £52.6m. Cloud transition driving ARR, efficiency, and margins. New regulatory standards and hybrid working boost record sales pipeline for FY24.
Read more